-
 The Red Lines In Your Business and Life ISR University
The Red Lines In Your Business and Life ISR University
ID: GweUMeV4XU
From:
-
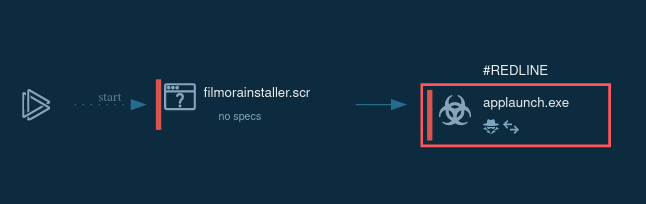
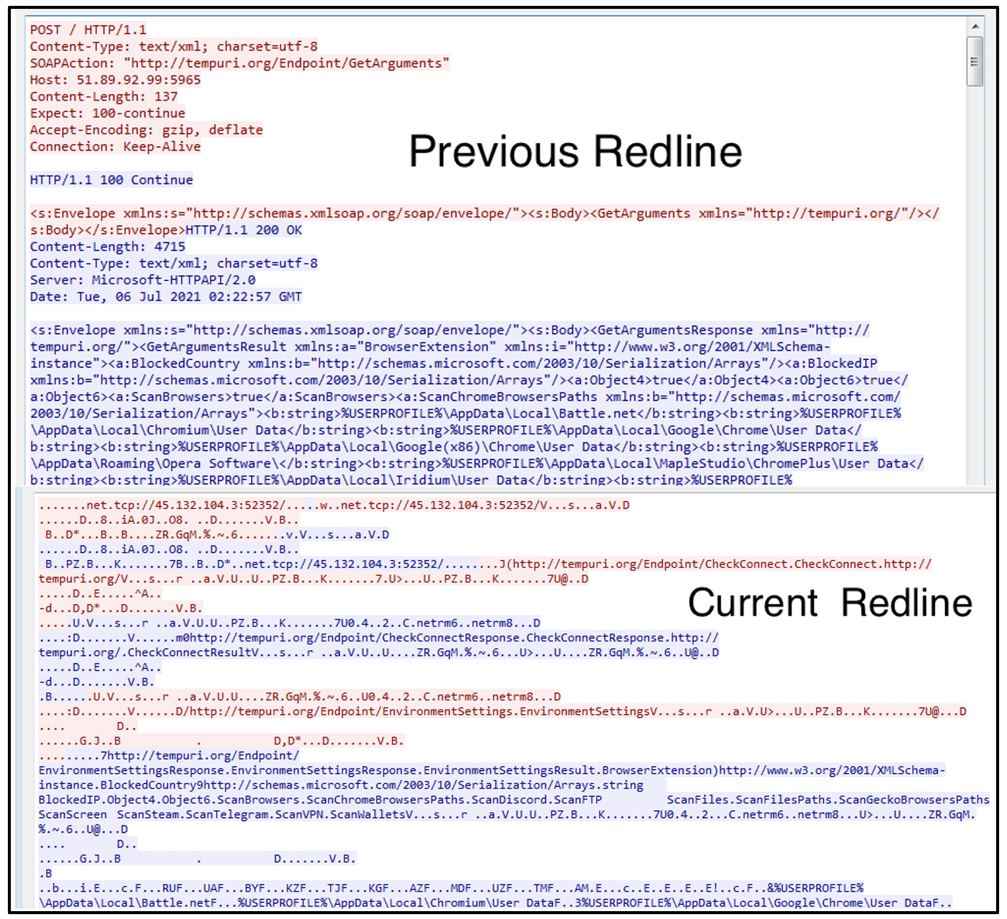 Threat Thursday: RedLine Update
Threat Thursday: RedLine Update
ID: jFgTilo2Eg
From:
-
 RedLine Analysis, by ANY.RUN
RedLine Analysis, by ANY.RUN
ID: vxLt5KVC9b
From:
-
 One The Race That Existed Atop The Red Line |
One The Race That Existed Atop The Red Line |
ID: FeYlZ2DxNz
From:
-
 Cyble A Deep-dive Analysis of Stealer Malware
Cyble A Deep-dive Analysis of Stealer Malware
ID: OTxEnpCEPs
From:
-
 Cyble A Deep-dive Analysis of Stealer Malware
Cyble A Deep-dive Analysis of Stealer Malware
ID: 3IciFjyegG
From:
-
 eSentire | Threat Intelligence Malware Analysis: Redline…
eSentire | Threat Intelligence Malware Analysis: Redline…
ID: t6GnW84kn6
From:
-
Detailed the RedLine Stealer | Research Report
ID: QUUcsWTerM
From:
-
 Mandiant Count Upon Security
Mandiant Count Upon Security
ID: zrc7FhIo8B
From:
-
Detailed the RedLine Stealer | Research Report
ID: Xs5hG2rEq2
From:
-
 About High-in-Demand Information Theft Tool: RedLine Stealer | Cyware and Analysis
About High-in-Demand Information Theft Tool: RedLine Stealer | Cyware and Analysis
ID: geAuPVEpSO
From:
-
 The Thin Line Summary and Analysis SparkNotes) | Book Notes
The Thin Line Summary and Analysis SparkNotes) | Book Notes
ID: WB7P3WAkuJ
From:
-
 eSentire | Threat Intelligence Malware Analysis: Redline…
eSentire | Threat Intelligence Malware Analysis: Redline…
ID: bSayZhR3D7
From:
-
 Behaviour Analysis of Redline Stealer -
Behaviour Analysis of Redline Stealer -
ID: X2g21RbyCy
From:
-
 Item analysis - Assessment Systems
Item analysis - Assessment Systems
ID: 1cdWTYN7Df
From:
-
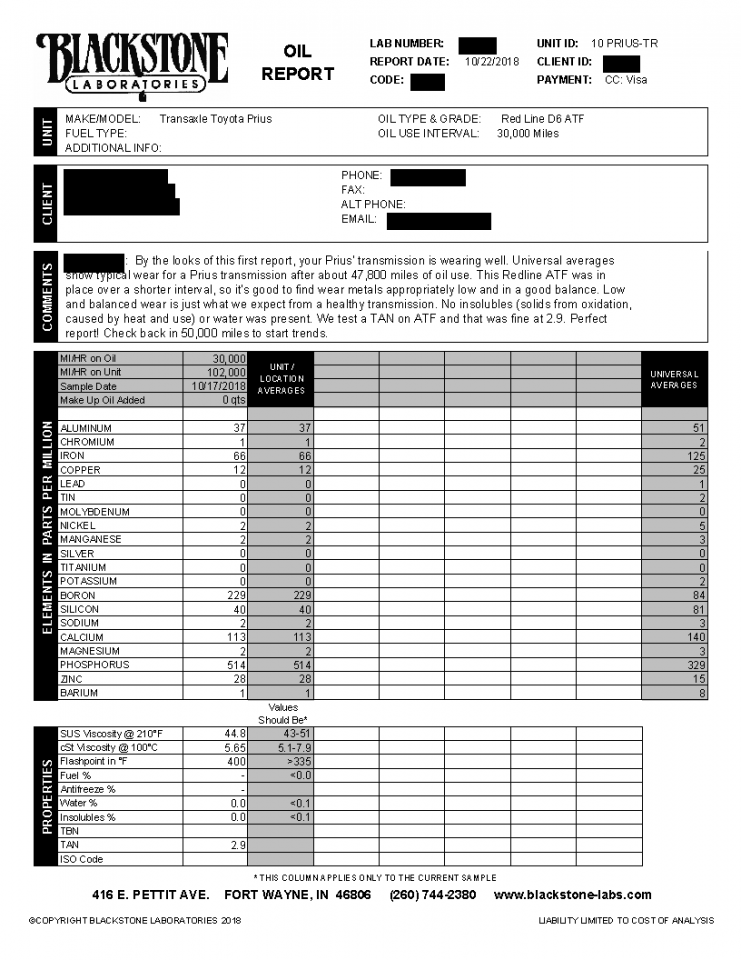 Oil Analysis, D6 ATF 30k miles PriusChat
Oil Analysis, D6 ATF 30k miles PriusChat
ID: l2cPWKLCTG
From:
-
 Rietveld X-Ray diffraction analysis of Ti-6Al-4V at GPa. The red... | Download Scientific Diagram
Rietveld X-Ray diffraction analysis of Ti-6Al-4V at GPa. The red... | Download Scientific Diagram
ID: O0eRyH5Ty4
From:
-
Learning by Beginning Memory Forensics - Redline -
ID: lkzdPKTs2T
From:
-
 analysis using redline Resources
analysis using redline Resources
ID: pbX42eQpJS
From:
-
 Analyse af Red Line Engelsk Opgaver.com
Analyse af Red Line Engelsk Opgaver.com
ID: Oxz20iVWZC
From:
-
 The red line indicates shear wave onset. The solid green line... | Download Scientific Diagram
The red line indicates shear wave onset. The solid green line... | Download Scientific Diagram
ID: hFCi0Owsr6
From:
-
 stealer Full analysis | Infosec Resources
stealer Full analysis | Infosec Resources
ID: bplaTjQJwU
From:
-
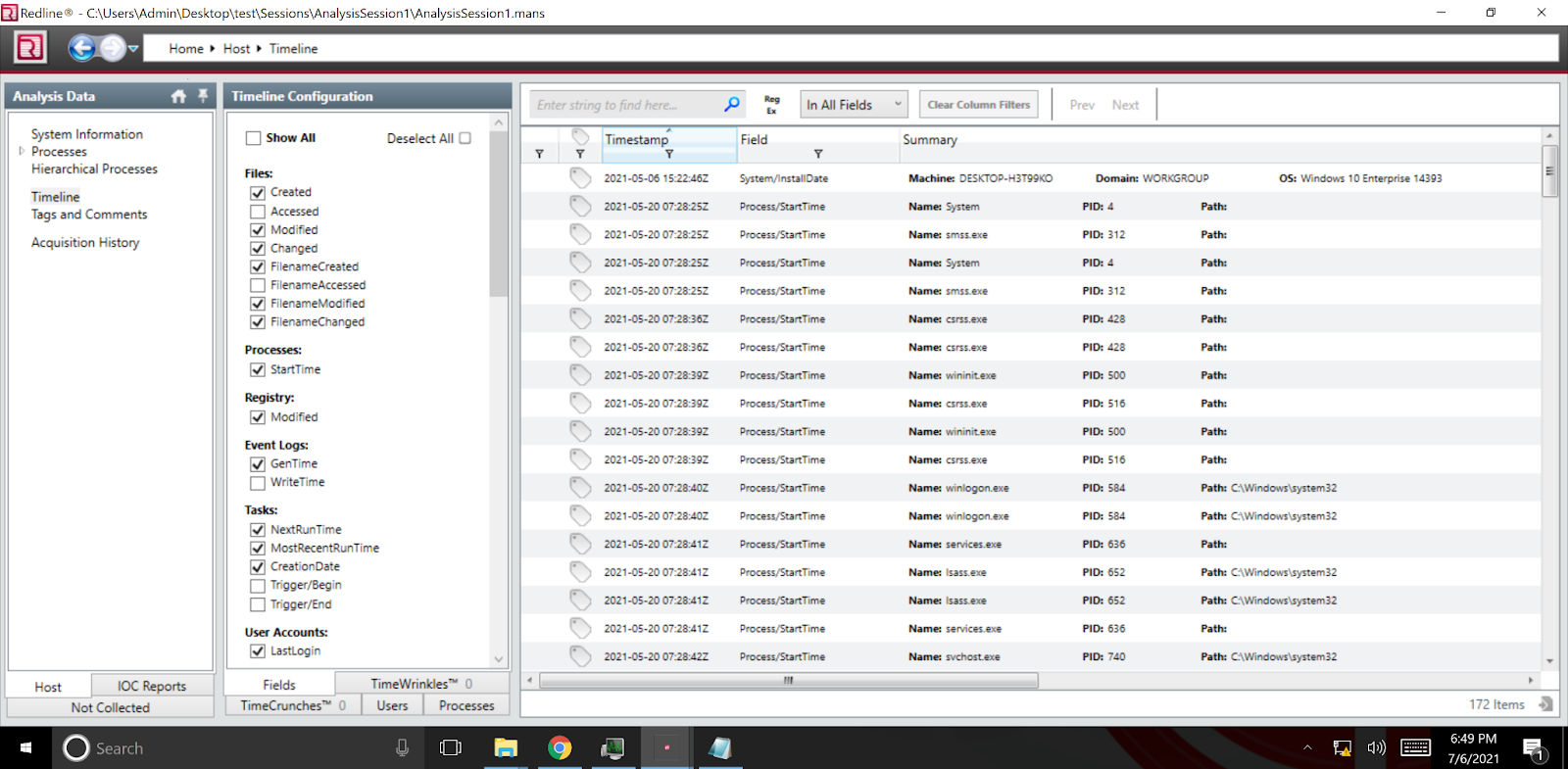 Forensics for Incident Response
Forensics for Incident Response
ID: YfXJA64MN8
From:
-
 analysis using redline Resources
analysis using redline Resources
ID: BQX4Do1B5r
From:
-
 Red – Sophie Hoffmann's Portfolio
Red – Sophie Hoffmann's Portfolio
ID: QwuSurce7h
From: